The Future of AI in Cybersecurity: Navigating AI-Driven Cyberattacks and Defenses
Estimated reading time: 9 minutes
Key Takeaways
- The future of AI in cybersecurity is a double-edged sword—empowering both attackers and defenders with unprecedented capabilities.
- AI enhances anomaly detection, automated responses, and threat hunting within SIEM platforms, but human oversight remains vital.
- Zero trust security models capitalize on AI for continuous verification, dynamic threat detection, and adaptive protections in shifting environments.
- Preparing for AI-driven cyberattacks requires layered strategies including AI governance, red-teaming, identity controls, and monitoring for AI model vulnerabilities.
- Quantum computing presents both risks and opportunities for AI security, demanding innovation in cryptography and identity management.
- Evolving AI regulation and governance frameworks are essential to ensure ethical AI use and compliance within cybersecurity operations.
- Future trends highlight increased AI agent dominance, hybrid quantum-AI solutions, and the necessity for human-AI collaboration to address complex challenges.
Table of contents
- Overview of Current AI Applications in Cybersecurity: AI in SIEM Platforms and Beyond
- AI and Zero Trust Security: Enhancing Continuous Verification
- Preparing for AI-Driven Cyberattacks: Strategies for Elevated Threats
- The Role of Quantum Computing and AI Security: Opportunities and Risks
- AI Regulation and Cybersecurity: Governance Taking Center Stage
- Future Trends and Predictions: What to Expect by 2026
- Conclusion: Advancing with Confidence in AI-Driven Cybersecurity
- Frequently Asked Questions
Overview of Current AI Applications in Cybersecurity: AI in SIEM Platforms and Beyond
Today, AI in SIEM platforms (Security Information and Event Management) plays a pivotal role in cybersecurity operations. SIEM systems leverage AI algorithms for multiple critical functions including:
- Anomaly detection: AI identifies unusual patterns in system logs or network traffic, impacting 72% of SIEM deployments.
- Novel threat identification: Machine learning models detect potential zero-day exploits and unknown threats dynamically.
- Automated response: Around 48% of organizations use AI to trigger immediate actions such as isolating infected hosts or blocking malicious IP addresses.
- Vulnerability management: 47% use AI to prioritize patching efforts and assess system weaknesses proactively.
The capabilities extend beyond these functions as organizations increasingly adopt semi-autonomous or fully autonomous AI agents. These agents can triage alerts, block threats at machine speed, and augment human-led functions such as penetration testing and patch deployment.
Despite growing automation, human expertise remains essential for contextual and strategic decision-making, ensuring AI-driven insights translate into effective security measures (source, source, source, source).
The future of AI in cybersecurity clearly involves integrating advanced AI agents within SIEM and other cyber defense platforms to enhance detection accuracy and response speed, countering increasingly sophisticated AI-driven cyberattacks.
AI and Zero Trust Security: Enhancing Continuous Verification
The zero trust security model is founded on the principle: “never trust, always verify.” It assumes that internal networks are no longer safe, requiring continuous identity and behavior verification regardless of location or device.
This approach has become crucial as traditional perimeter defenses dissolve due to cloud-native applications and SaaS tools replacing on-premises infrastructure.
AI significantly enhances zero trust security by enabling:
- Dynamic threat detection that continuously analyzes real-time data feeds. This allows the system to adjust defenses rapidly based on evolving threats.
- Adaptive protections utilizing global telemetry to anticipate exploits proactively rather than simply reacting.
- Continuous monitoring architectures that can predict and pre-empt attack vectors.
This AI-powered zero trust approach aligns with priorities for cybersecurity leaders, with 65% identifying Security Operations Center (SOC) optimization—strengthened through AI-enabled zero trust—as a top focus.
Implementing AI-driven zero trust frameworks improves defense agility and resilience, particularly in cloud and hybrid environments where attack surfaces constantly shift (source, source, source).
Preparing for AI-Driven Cyberattacks: Strategies for Elevated Threats
As AI enhances cyber offense capabilities, AI-driven cyberattacks escalate in complexity and scale. Threats include:
- Hyper-personalized phishing targeting individuals with convincing, context-aware lures—a top concern for 50% of security professionals.
- Automated chaining of exploits, where AI systems link vulnerabilities dynamically, facilitating multi-stage attacks (45% concern).
- Adaptive malware that continuously evolves by modifying its code to evade detection (40%).
- Deepfake voice fraud, leveraging AI-generated synthetic voices to manipulate individuals or social engineering (40%).
- Fully orchestrated attacks requiring minimal human intervention due to automation.
Organizations must proactively prepare by implementing robust strategies:
- AI governance tools, such as “AI firewalls,” to block prompt injection attacks targeting AI systems themselves.
- Continuous AI red-teaming exercises simulate adversarial scenarios to expose weaknesses and harden AI model defenses.
- Identity controls deployed by 60% of organizations to safeguard access and authentication.
- Data loss prevention (DLP) systems, used by 54%, protect sensitive information from being exfiltrated.
- Monitoring AI models for poisoning or shadow agent behavior, with 42% of organizations tracking these risks.
These defense mechanisms must operate at machine speed to match the velocity of automated threat evolution, ensuring rapid detection and mitigation before damage occurs (source, source, source).
Preparing for AI-driven cyberattacks requires a comprehensive, layered strategy combining technology, governance, and continuous vigilance.
The Role of Quantum Computing and AI Security: Opportunities and Risks
Quantum computing is an emerging technology with the potential to disrupt cybersecurity by breaking traditional cryptographic algorithms that underpin current AI security models and encrypted communication.
Key points on quantum computing’s impact:
- Threat to AI security: Quantum machines could decipher most widely used encryption, jeopardizing data confidentiality and AI model integrity.
- Security enhancement: At the same time, quantum computing accelerates simulations, optimizations, and predictive analytics, which can massively improve threat detection and mitigation at scale.
- Challenges: The combination of quantum technology and AI creates new vulnerabilities. For example, “black box” AI models become more susceptible to data poisoning and adversarial attacks when quantum-powered adversaries analyze model behaviors.
- Evolving identity management: Quantum-AI convergence demands advanced solutions for identity and access control, capable of handling increased cryptographic complexity.
Moreover, geopolitical risks intensify as nation-states develop quantum and AI capabilities, raising concerns about cyber warfare and espionage.
Organizations must anticipate these shifts by adopting proactive cybersecurity mitigations and evolving strategies that embrace both quantum innovation and AI robustness (source, source, source, source).
AI Regulation and Cybersecurity: Governance Taking Center Stage
The landscape of AI regulation and cybersecurity is transforming quickly. Regulatory bodies now prioritize:
- AI governance frameworks mandating clear policies for ethical AI use.
- Continuous security posture management requiring ongoing evaluation and reporting of AI risks.
- Mandatory disclosures regarding AI vulnerabilities and data privacy impacts.
Cyber insurance providers and privacy regulators increasingly influence how organizations develop and deploy AI in security roles. These regulatory pressures drive a push toward:
- Formalized AI policies, yet 63% of organizations still lack such governance.
- Implementation of ethical automation safeguards to ensure AI decisions align with organizational values and compliance.
- Building trust through compliance measures embedded within cloud migration strategies.
This evolving regulatory environment compels organizations to integrate AI governance as a foundational element of their cybersecurity approaches to maintain operational resilience and legal compliance (source, source, source).
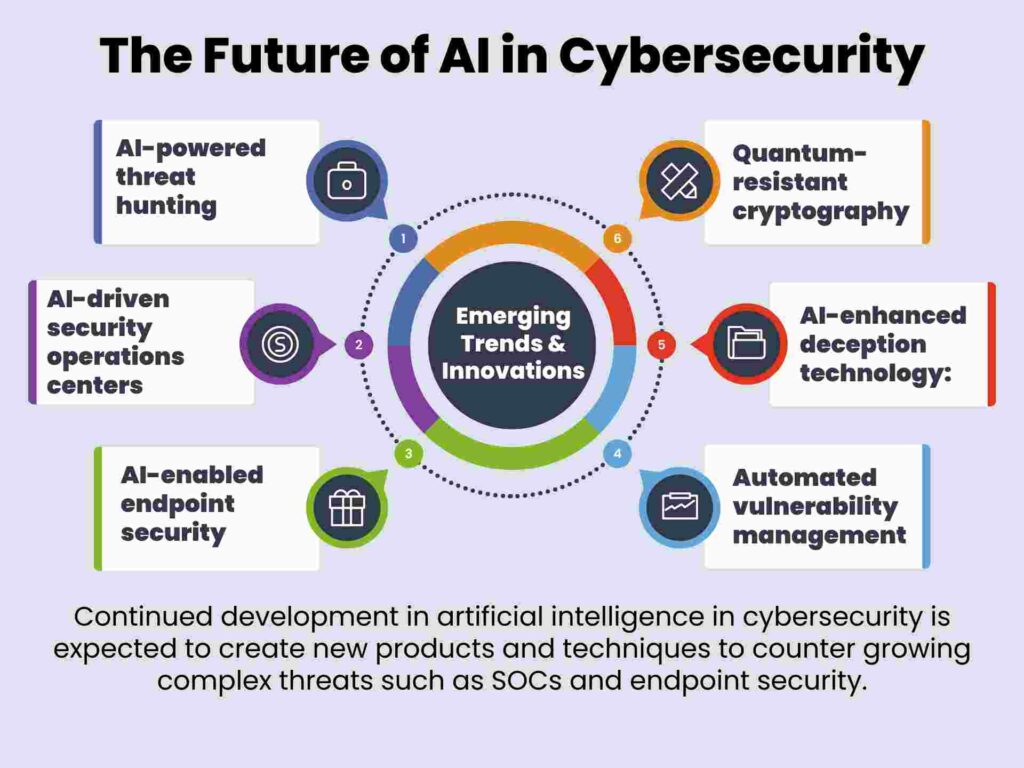
Future Trends and Predictions: What to Expect by 2026
Looking ahead, several trends will shape the future of AI in cybersecurity by 2026:
- Dominance of AI agents: Offensive operations will increasingly target AI systems themselves, while defensive SOCs will rely on AI agents performing continuous, cloud-native monitoring and threat hunting.
- Innovations such as:
- Predictive patching using AI to identify vulnerabilities before exploitation.
- AI-orchestrated automated workflows improving response efficiency.
- Hybrid quantum-AI security solutions enhancing encryption and detection.
- Challenges including:
- Trust gaps, with only 14% of organizations allowing independent AI remediation actions.
- Expanded attack surfaces due to widespread AI adoption and shadow AI systems.
- Need for robust human-AI collaboration models to balance automation with context-aware decision-making.
- Recommended best practices:
- Prioritize AI-human augmentation to maximize strengths of both.
- Accelerate adoption of AI governance frameworks (currently emphasized by 57%).
- Deploy cloud-centric continuous monitoring tools to manage risks from shadow AI and equity issues.
These developments underscore that cybersecurity will be defined by AI’s dual capacity to innovate defenses and escalate offense, requiring organizations to stay agile and ahead of evolving threats (source, source, source).
Conclusion: Advancing with Confidence in AI-Driven Cybersecurity
The future of AI in cybersecurity will be defined by rapid technological evolution where AI-driven cyberattacks escalate in speed, scale, and coordination while AI-enhanced defenses multiply efficiency and resilience.
To navigate this dual-edged reality, organizations must:
- Assess their current AI security posture rigorously.
- Implement comprehensive AI governance guardrails.
- Embed continuous machine-speed monitoring for real-time defense adaptability.
By acting strategically on the insights presented here, security teams can prepare confidently for the shifts ahead, turning the challenges of AI-driven cyber threats into an opportunity to build stronger, smarter, and more adaptive defenses.
The time to prepare for the future of AI in cybersecurity is now.
Frequently Asked Questions
- What are the primary benefits of AI in cybersecurity?
- AI enhances cybersecurity by enabling faster anomaly detection, automated responses, threat hunting at scale, and improving the accuracy of identifying novel threats. It allows security operations to keep pace with the evolving threat landscape.
- How does AI improve zero trust security models?
- AI supports continuous verification by dynamically analyzing behavior and identity data, adapting defenses based on real-time threat intelligence, and enabling proactive detection and response—key to maintaining trust in rapidly shifting environments.
- What strategies help organizations prepare for AI-driven attacks?
- Organizations should implement AI governance and firewall tools, conduct continuous AI red-teaming, deploy robust identity controls, implement data loss prevention, and monitor AI models for adversarial behaviors to counter increasingly sophisticated AI-driven threats.
- How does quantum computing impact AI and cybersecurity?
- Quantum computing threatens existing cryptographic standards by potentially breaking widely used encryption, jeopardizing data confidentiality and AI model integrity. Simultaneously, it offers advanced simulation and analytics that can enhance cybersecurity if integrated effectively.
- Why is AI governance important in cybersecurity?
- AI governance ensures ethical and compliant use of AI within cybersecurity, managing risks such as bias, vulnerability to adversarial attacks, and regulatory compliance, thereby protecting operational resilience and stakeholder trust.