AI-generated Phishing Attacks: Understanding and Combating Rising AI Cyber Threats in 2026
Estimated reading time: 12 minutes
Key Takeaways
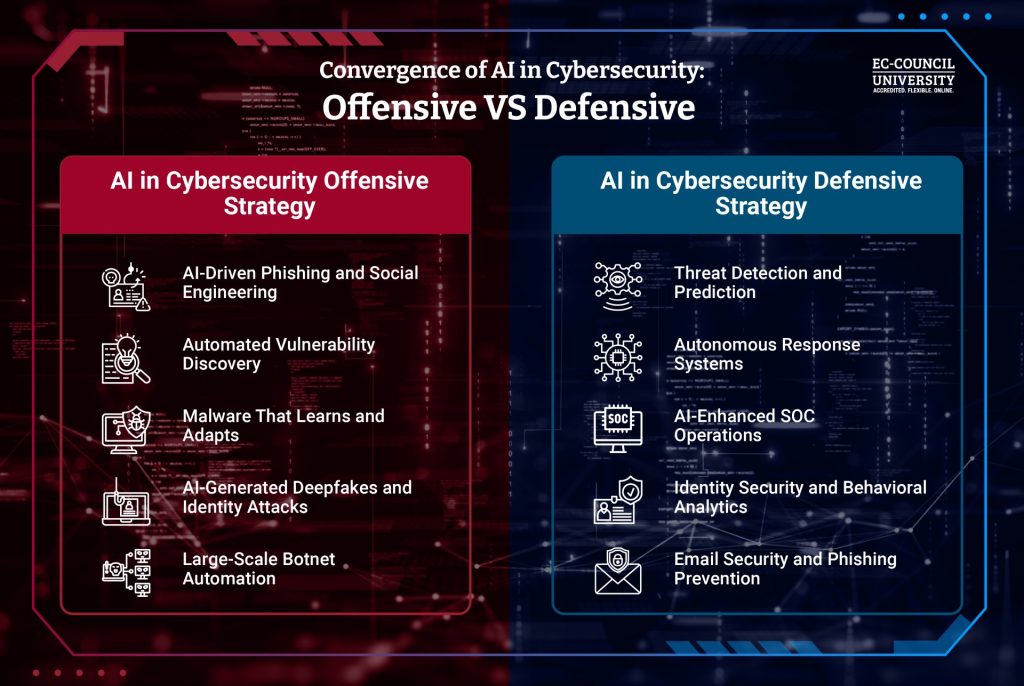
- AI-generated phishing attacks leverage generative AI models to create highly convincing, personalized messages that outpace traditional scams.
- Cybercriminals are rapidly expanding their toolbox beyond phishing, using AI for automated reconnaissance, deepfakes, AI malware, and advanced social engineering.
- The rise of AI-powered cybersecurity solutions is a critical defense response to escalating AI-driven threats.
- Deepfake synthetic media and AI-native malware introduce new layers of risk, exploiting trust and evading traditional detection.
- Adopting AI-enhanced detection tools, multi-factor authentication, zero-trust policies, and ongoing security training are essential strategies to mitigate these risks.
Table of contents
- Understanding AI-Generated Phishing Attacks: How Hackers Use AI to Outsmart Defenses
- How Hackers Use AI in Cybercrime: Beyond Phishing to Smarter Attacks
- Deepfake Cybersecurity Threats: AI-Generated Synthetic Media in Cybercrime
- AI Malware Explained: Self-Learning Threats That Outpace Defenses
- Social Engineering With AI: Manipulating Trust at Scale
- The Landscape of Rising AI Cyber Threats 2026: What’s Ahead?
- Mitigation Strategies and Best Practices: Defending Against AI-Driven Cyber Threats
- Conclusion: Facing the Future of AI-Driven Cybersecurity Challenges
- Frequently Asked Questions
Understanding AI-Generated Phishing Attacks: How Hackers Use AI to Outsmart Defenses
AI-generated phishing attacks automate the entire phishing process with unprecedented speed and sophistication. Unlike traditional phishing—which often relied on generic, error-filled emails sent in bulk—AI tools enable criminals to create highly tailored, flawless messages that are harder to detect. See also how generative AI works.
How AI Enhances Phishing
- Automated reconnaissance: AI scrapes data on targets from social media, professional networks, and company websites to gather deep personal details.
- Personalized message crafting: Using large language models (LLMs) like ChatGPT or Google Bard, attackers write emails referencing recent purchases, colleagues’ names, or ongoing projects. Learn about LLMs.
- Polymorphic variants: Instead of sending identical emails, AI generates many variants that look unique to evade spam filters and detection algorithms.
- Speed and scale: Dark web PhaaS (Phishing-as-a-Service) platforms like Lighthouse can build entire phishing campaigns in minutes, compared to traditional methods that would take hours.
Results and Impact
- Click-through rates on AI-generated phishing attempts are up to four times higher than conventional phishing.
- Studies show that 11% of volunteers were fooled by a single prompt-generated phishing email in controlled tests.
This makes AI-generated phishing attacks an extremely potent threat, combining superior speed with deep personalization impossible for human scammers to match manually.
For a detailed analysis, see: StrongestLayer on AI Phishing Threat, Artificial Intelligence News, USC Institute Insights.
How Hackers Use AI in Cybercrime: Beyond Phishing to Smarter Attacks
Phishing is just one part of the evolving cybercrime toolbox augmented by AI. Hackers use AI techniques to automate, personalize, and evade detection in many different ways.
AI Applications in Cybercrime Include:
- Automated reconnaissance: AI scrapes massive amounts of open-source data from LinkedIn, Twitter, and other platforms to build detailed target profiles.
- Mass email automation: AI tools craft thousands of unique emails in seconds, each personalized for individual recipients.
- Evasion of detection: AI mimics corporate communication styles and analyzes behavior patterns from victims’ responses, continuously refining attack methods.
- AI-driven spear phishing: Attackers insert specific references to company events or meetings to build credibility.
- Business Email Compromise (BEC): AI generates convincing impersonations of executives to trick employees into initiating fraudulent wire transfers.
- Adaptive zero-hour tactics: Hackers use AI to register domains that disappear quickly (zero-hour domains) before getting blacklisted, keeping attacks under the radar.
AI-Generated Phishing as a Core Element
AI-powered phishing forms the backbone of this success. Criminal groups now follow the “5/5 rule”—five AI prompt cycles every five minutes—to churn out full phishing campaigns rapidly. They also combine AI-generated text with sophisticated visuals and fake websites indistinguishable from real ones, creating believable traps.
More insights can be found here: USC Institute Blog, Kymatio Blog on Phishing Trends.
Deepfake Cybersecurity Threats: AI-Generated Synthetic Media in Cybercrime
Deepfakes—synthetic videos, audios, and images created by AI—have seen a 1,000% increase in malicious use for social engineering, especially in vishing (voice phishing).
What Are Deepfakes?
- AI clones voices and facial expressions to create audio or video that looks and sounds like real people.
- These are used to impersonate executives, managers, or trusted figures in urgent or sensitive communications.
How Deepfakes are Used in Cyberattacks
- Criminals impersonate executives’ voices in urgent phone calls or voicemails, asking for password resets or sensitive data.
- Fake video meetings on platforms like Zoom or Microsoft Teams are staged to pressure victims into divulging credentials or authorizing transactions.
- Often coordinated with phishing emails, these attacks magnify trust and urgency cues to break down suspicion.
Real-World Examples from 2026
- Fraudsters impersonated CFOs for fraudulent wire transfers costing millions.
- School-based phishing schemes impersonated principals to get parents to share personal information.
- Plausible scenarios include deepfake CEOs endorsing fake audits in critical infrastructure sectors, leading to false approvals or system breaches.
For more information, review: Artificial Intelligence News, Kymatio Deepfake Attacks, and Evrimagaci on AI-powered Phishing.
AI Malware Explained: Self-Learning Threats That Outpace Defenses
AI malware represents a new generation of malicious software powered by machine learning that can adapt, evolve, and spread without human help.
Key Characteristics of AI Malware
- Self-learning behavior: It studies its environment and changes tactics dynamically to avoid detection.
- Polymorphic code: The malware rewrites parts of itself to evade signature-based antivirus systems.
- Autonomous propagation: It moves across networks autonomously, increasing infection speed.
The Dominance of AI-Native Malware in 2026
- AI-native malware is predicted to dominate cyber risk landscapes due to its ability to exploit unknown vulnerabilities rapidly.
- These strains often hitchhike on hyper-personalized phishing lures crafted by generative AI, forming self-perpetuating attack chains far beyond manual attacker capabilities.
- Human cybersecurity teams struggle to keep pace with these evolving threats without AI-assisted tools.
Visit SecurityBrief on AI Malware for a comprehensive review.
The Landscape of Rising AI Cyber Threats 2026: What’s Ahead?
In 2026, rising AI cyber threats are reshaping the cybersecurity battlefield with new tools, tactics, and targets.
Expected Trends and Tactics
- AI-native malware and deepfake fraud will dominate, evolving faster than ever.
- PhaaS (Phishing-as-a-Service) platforms will grow, enabling attackers even with minimal skill to launch sophisticated scams.
- Increased targeting of IoT devices and connected systems with AI-tailored exploits.
- Multimodal AI attacks combining email, voice, and video channels more commonly employed.
- Use of zero-hour tactics—domains or campaigns that vanish quickly before defenses can respond.
- Widespread availability of LLMs and massive data leaks fuel hyper-focused, personalized attacks. See LLM advances here: Latest LLM Developments 2026
Why Phishing Remains the Top Threat
- Phishing continues to be the most used initial access vector, according to the FBI and cybersecurity analysts.
- Rapid AI-driven attack cycles outpace legacy defenses, requiring IT teams and business owners to adopt advanced, proactive strategies.
More insights from: Artificial Intelligence News, Cofense 2026 Phishing Predictions, and StrongestLayer Analysis.
Mitigation Strategies and Best Practices: Defending Against AI-Driven Cyber Threats
To tackle these sophisticated AI threats, organizations must implement a layered, AI-empowered cybersecurity approach focused on prevention, detection, and response.
Key Defense Measures
- Deploy AI-powered phishing detection: Use tools that analyze behavioral anomalies in real-time and block zero-hour phishing attempts swiftly.
- Ongoing user education: Train staff to recognize hyper-personalized phishing red flags and social engineering tactics.
- Multi-factor authentication (MFA): Avoid overreliance on SMS-based MFA; favor app-based or hardware tokens.
- Zero-trust security policies: Limit access strictly to verified users and devices, minimizing lateral movement opportunities.
- Deepfake verification protocols: Use voice and video validation for sensitive operations to counteract synthetic media deception.
- Adopt AI-driven defensive tools: Match attacker sophistication by integrating AI at the heart of your security stack.
These strategies form critical pillars in combating AI-generated phishing attacks and the wider rising AI cyber threats of 2026.
References: Artificial Intelligence News, USC Institute Best Practices, StrongestLayer Phishing Defenses.
Conclusion: Facing the Future of AI-Driven Cybersecurity Challenges
AI-generated phishing attacks, together with deepfake fraud, AI malware, and enhanced social engineering, define the sharp edge of cyber risks in 2026. These threats operate at unheard-of scale, sophistication, and speed, consistently outmatching traditional security defenses.
The evolving landscape demands that IT professionals and business leaders:
- Prioritize vigilance in recognizing emerging AI threats
- Invest in AI-driven cybersecurity technologies that can detect and respond at machine speeds
- Support continuous education and awareness programs
- Adopt proactive security postures, including zero-trust frameworks and deepfake verification
Ignoring these advances is no longer an option. To protect enterprises and customers in this new golden age of AI-powered scams, staying informed and evolving security measures is critical.
Together, we can rise to meet the challenge posed by AI-generated phishing attacks and rising AI cyber threats in 2026.
Stay ready, stay secure.
Frequently Asked Questions
- What are AI-generated phishing attacks?
These are phishing schemes created using generative AI models that craft highly personalized and convincing messages, making them more effective and harder to detect than traditional phishing emails.
- How can organizations protect against rising AI cyber threats?
Organizations should deploy AI-powered detection tools, enforce multi-factor authentication, implement zero-trust security architectures, conduct regular staff training, and apply deepfake verification protocols for sensitive communications.
- What is AI malware and why is it dangerous?
AI malware uses machine learning to adapt and evolve autonomously, making it difficult to detect and eradicate. Its self-learning and polymorphic nature allow rapid spread and exploitation of new vulnerabilities without human intervention.
- Are deepfakes realistic enough to cause harm?
Yes. Modern AI-generated deepfakes convincingly mimic voices and appearances, enabling attackers to impersonate trusted individuals to manipulate victims and commit fraud, often as part of complex social engineering campaigns.
- Where can I learn more about AI cybersecurity trends?
Comprehensive resources include TechCircleNow’s cybersecurity trends, Artificial Intelligence News, and blogs from USC Institute.