RSA vs Black Hat vs DEF CON: A Detailed Security Event Comparison for Cybersecurity Conferences
Estimated reading time: 12 minutes
Key Takeaways
- The comparison of RSA vs Black Hat vs DEF CON is essential for anyone navigating the cybersecurity landscape.
- RSA Conference focuses on corporate strategy, leadership, and industry-wide cybersecurity trends.
- Black Hat offers highly technical content, vulnerability disclosures, and advanced trainings for practitioners.
- DEF CON fosters a grassroots hacker culture with hands-on workshops, competitions, and informal collaboration.
- Each conference has distinct audiences, atmospheres, and networking styles, impacting career goals and learning experiences.
Table of contents
- Overview of the Three Conferences: RSA vs Black Hat vs DEF CON
- Key Aspects for Comparison: A Comprehensive Security Event Comparison
- Use Cases and Who Should Attend Each Conference
- Summary Table: Clear Visual Security Event Comparison – RSA vs Black Hat vs DEF CON
- Conclusion: Navigating RSA vs Black Hat vs DEF CON in Cybersecurity Conferences
- Call to Action
- Frequently Asked Questions
Overview of the Three Conferences: RSA vs Black Hat vs DEF CON
Before delving into details, it’s crucial to understand the unique identities of each conference.
RSA Conference: The Industry Giant
The RSA Conference is a large-scale, established event that draws roughly 50,000 attendees each year in San Francisco (source). Positioned as a strategic forum, RSA focuses on broad cybersecurity trends, leadership, and industry-wide challenges. Its reputation as a gathering spot for executives, security professionals, and vendors makes it a pivotal event for steering corporate cybersecurity strategies and building business partnerships.
Black Hat: The Technical Deep Dive
Black Hat is a mid-sized but highly technical cybersecurity conference typically held in Las Vegas, with additional global editions. Attracting security researchers, analysts, and ethical hackers, Black Hat is renowned for its in-depth presentations, cutting-edge vulnerability disclosures, and specialized training sessions (source). It serves as a hub for practitioners seeking hands-on technical mastery and exposure to the latest security research breakthroughs.
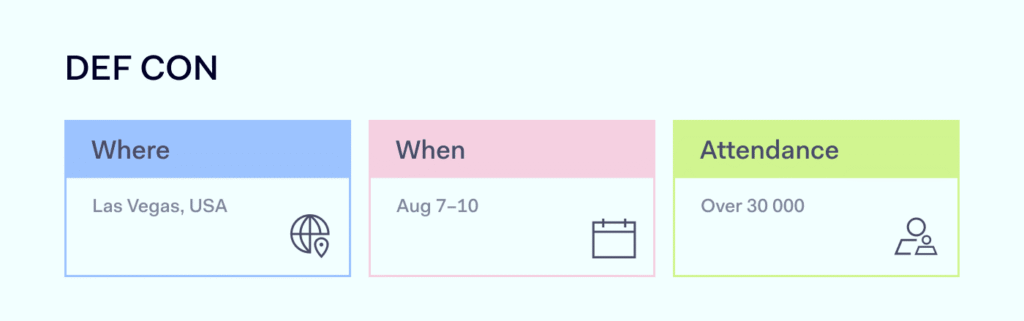
DEF CON: The Hacker Community Epicenter
Following Black Hat in Las Vegas, DEF CON stands as the world’s largest gathering of hackers, hobbyists, and grassroots security enthusiasts (source). Unlike the others, DEF CON thrives on an informal, playful culture. It features hands-on Capture The Flag (CTF) competitions, “villages” dedicated to specific hacking disciplines like hardware and OSINT, and open forums encouraging experimental learning. DEF CON is where the hacker community converges to innovate, collaborate, and challenge norms.
This RSA vs Black Hat vs DEF CON overview highlights the spectrum of cybersecurity conferences—from corporate strategy to technical research to grassroots hacking culture.
Key Aspects for Comparison: A Comprehensive Security Event Comparison
1. Audience and Community
- RSA Conference Audience
RSA predominantly attracts a corporate crowd: CISOs, security executives, vendors, and professionals focused on industry strategy and partnership opportunities (source, source). The environment suits those interested in leadership, governance, compliance, and vendor relationships. - Black Hat Audience
Black Hat targets technical professionals like security researchers, analysts, and ethical hackers who demand highly detailed, technical content. Its community thrives on vulnerability research, exploit development, and defensive tactics (source, source). - DEF CON Audience
DEF CON is eclectic and inclusive, welcoming hackers, hobbyists, federal agents, and anyone with a passion for hands-on security exploration. It fosters a relaxed, open community with a culture that thrives on informal collaboration and hacking experimentation (source, source).
This contrast in audiences is a core driver in the overall security event comparison, shaping the tone and content of each conference’s experience.
2. Content and Sessions
- RSA Conference Content
RSA leans on high-level keynotes and panel discussions tackling business impact, regulatory issues, and broad cybersecurity trends such as digital transformation and cloud security (source, source). The content is strategic and less technical. For more on digital transformation trends relevant to RSA’s focus, see digital transformation strategy guide. - Black Hat Content
The conference offers deep-dive briefings, advanced training courses, and disclosures of newly discovered vulnerabilities (source, source). Sessions emphasize hands-on technical skills and cutting-edge security research applicable to practitioners. For broader cybersecurity trends including threat detection, refer to top cybersecurity trends 2025. - DEF CON Content
DEF CON’s sessions include workshops, CTF competitions, and dedicated villages focusing on niche hacking topics like hardware exploiting or OSINT gathering. Demonstrations push practical learning in an engaging, informal format (source, source). For an overview of hands-on hacking and CTF approaches, see conference reporting checklist guide.
This stark difference in content highlights the multidimensional nature of cybersecurity conferences today, making this security event comparison especially relevant.
3. Networking Opportunities
- RSA Networking
RSA’s extensive hall features vendors, recruiters, and executive networking designed for career development and business partnerships (source). It presents formal, high-level interaction opportunities. Effective networking strategies can be explored at how to network in tech guide. - Black Hat Networking
Black Hat fosters professional connections among security researchers and practitioners, serving as a gateway to the more informal DEF CON scene (source, source). - DEF CON Networking
DEF CON excels at casual, organic networking in competitions, social events, and informal meetups. The environment encourages idea exchanges and collaboration anchored in a relaxed culture (source, source).
These varied networking dynamics are a crucial factor in the RSA vs Black Hat vs DEF CON decision-making process.
4. Event Scale and Location
| Aspect | RSA | Black Hat | DEF CON |
|---|---|---|---|
| Size | ~50,000 attendees (source) | Several thousand attendees (source) | Massive, grassroots attendance (source) |
| Location | San Francisco, USA (source) | Las Vegas, USA (main); global offshoots (source) | Las Vegas, USA (post-Black Hat) (source) |
| Timing | Spring annually (source) | Early August (US) (source) | Early August immediately after Black Hat (source) |
This scale and location comparison serves as a quick guide when choosing what fits your schedule and travel preferences.
5. Cost and Accessibility
- RSA Conference Cost
RSA tickets are generally on the higher end, with options for virtual attendance making it somewhat accessible remotely (source). - Black Hat Cost
Black Hat’s technical briefings can cost upwards of $2,500, with specialized trainings adding several thousand dollars more (source). - DEF CON Cost
DEF CON remains affordable at approximately $450-$500, remarkable for an event of its scale. Admission is typically cash-only at the door, reflecting its grassroots ethos (source).
Cost plays a decisive role in accessibility and should factor heavily in your security event comparison.
6. Atmosphere and Culture
- RSA Atmosphere
RSA maintains a formal, professional setting geared for learning and official networking (source, source). - Black Hat Atmosphere
Black Hat is polished, intense, and deeply research-focused, serving serious practitioners and academics (source). - DEF CON Atmosphere
DEF CON is informal, energetic, and sometimes chaotic — a “hacker paradise” fostering creativity, collaboration, and hands-on experimentation (source, source).
This cultural difference greatly affects the attendee experience and learning style.
7. Industry Impact and Reputation
- RSA shapes industry-wide strategic trends and thought leadership (source).
- Black Hat drives forefront research disclosures and technical breakthroughs (source).
- DEF CON fuels innovation in hacking techniques and grassroots security education (source).
Together, they represent a combined legacy that defines cybersecurity’s past, present, and future.
Use Cases and Who Should Attend Each Conference
Understanding your own role and goals helps determine the best conference to attend.
- RSA Conference: For Executives and Strategic Leaders
Ideal if you are a security executive, corporate professional, or vendor seeking industry insights, building leadership skills, or forming business partnerships (source, source). - Black Hat: For Technical Researchers and Practitioners
Perfect for security analysts, penetration testers, and researchers wanting deep technical training and access to zero-day vulnerability disclosures (source, source). - DEF CON: For Hackers, Hobbyists, and Hands-On Enthusiasts
Best suited for those passionate about immersive workshops, hacking challenges, and community-driven learning, including students and grassroots hackers (source, source).
This targeted guidance is essential for navigating the RSA vs Black Hat vs DEF CON landscape.
Summary Table: Clear Visual Security Event Comparison – RSA vs Black Hat vs DEF CON
| Feature | RSA Conference | Black Hat | DEF CON |
|---|---|---|---|
| Primary Focus | Strategy, leadership, industry trends (source) | Technical research, briefings (source) | Hacking culture, contests, hands-on learning (source) |
| Typical Audience | Executives, CISOs, vendors (source) | Researchers, analysts, practitioners (source) | Hackers, hobbyists, federal agents (source) |
| Event Vibe | Formal, professional (source) | Intense, polished, research-driven (source) | Informal, chaotic, community-rich (source) |
| Cost (USD) | High, with virtual options (source) | $2,500+ for briefings, training extra (source) | ~$450-$500 cash only (source) |
| Location & Timing | San Francisco, Spring (source) | Las Vegas, Early August US main (source) | Las Vegas, Early August following Black Hat (source) |
| Best Suited For | Executives, corporate strategy, networking (source) | Technical mastery, vulnerability research (source) | Hacker culture, hands-on skills, community (source) |
This table encapsulates the essential elements of the RSA vs Black Hat vs DEF CON comparison, supporting readers in making an informed choice.
Call to Action
What’s your experience with RSA vs Black Hat vs DEF CON? Share your insights or questions in the comments below to join the conversation. For deeper preparation and tips, explore our related guides on maximizing cybersecurity conferences in 2026 and beyond, including the latest in cybersecurity trends and how AI is reshaping cybersecurity at how AI is used in cybersecurity.
Frequently Asked Questions
- What is the main difference between RSA, Black Hat, and DEF CON?
RSA focuses on corporate strategy and leadership; Black Hat offers technical research and training; and DEF CON is a grassroots hacker community event emphasizing hands-on learning and contests.
- Who should attend each conference?
Executives and professionals benefit most from RSA, technical researchers and practitioners from Black Hat, and hackers, hobbyists, and students from DEF CON.
- How expensive are these conferences?
RSA has a high price point but offers virtual attendance; Black Hat can exceed $2,500 with training; DEF CON is the most affordable at around $450-$500, usually cash-only.
- Are these conferences held in the same location?
RSA is held in San Francisco annually during spring. Black Hat and DEF CON are both held in Las Vegas in early August, with DEF CON following immediately after Black Hat.
- Can I attend more than one conference?
Yes. Many attendees go to Black Hat for the technical briefings and then attend DEF CON for its hands-on and community-driven activities to gain the full spectrum of experiences.